Brands
An Enhanced Drone Technical Forensic Investigation Process Using a Yuneec Typhoon H
Remotely Piloted Aerial Systems (RPAS) technology, which includes drones, find applications in almost all aspects of modern living. Drone operations by bad actors resulting in malpractices like- invasion of privacy, drug smuggling or terrorist activities are on the rise. Additionally, drone crashes and incidents raise significant concerns. Potential real-world threats posed by extensive use of RPAS technology would require defensible and admissible forensic evidence to be presented in the courts of law in case of a rogue drone incident.
In new research by a team of researchers from the Department of Computer and Information Technology, Purdue University, a technical forensic process comprising a ten step approach to reduce the complexity of the identification and investigation of drones has been proposed. Using the proposed technical process, drone images is analyzed using the Computer Forensics Reference Datasets (CFReDS) and the Typhoon H aerial vehicle manufactured by Yuneec, Inc. for demonstration. The paper further explores the availability and value of digital evidence that would allow a more practical digital investigation to be able to build an evidence-based experience.
Contributions of the Paper
- This paper introduces an enhanced Drone Technical Forensic Investigation Process based on acquired drone data from different components of the Typhoon H.
- This paper creates a standardized approach to conduct a digital forensic analysis of a drone using the outcome of this research by proposing a digital forensic investigation into technical processes for drones.
- This paper utilizes validation and verification methods for the forensics analysis of drones. It is important to note that the validation process is critical to meet the standards of a legitimate digital forensics investigation. Therefore, several tools were tested in relation to the analysis of digital evidence found in drone components.
- The research efforts that are discussed concentrate on the extraction of data from different types of drones. The process presented in this paper integrates the forensic analysis of the RPAS into a technical process that can be applied to wide range of drones with similar storage mechanisms and functionality. Nevertheless, there could be different cases where drones are customized, hence require in-depth analysis and further studies.
Researchers Fahad E. Salamh, Umit Karabiyik and Marcus K. Rogers propose the technical process identifies “preparation” as the first phase, which describes the preparation of digital evidence to include a collection of electronic devices at the crime scene. The next phase is the identification of both physical and digital evidence. This phase identifies the types of digital evidence including the classification of the drone. The third phase is where the forensics investigation commences, either on all components of the drone or on some of them. Based on the third phase, there will be subsequent technical steps that will need to be followed in order to achieve a complete and forensically sound report. Phases 4–10 primarily concentrate on the analysis of outcomes during the investigation, which, if adhered to, can result in a successful and forensically sound collection of evidence and reporting.
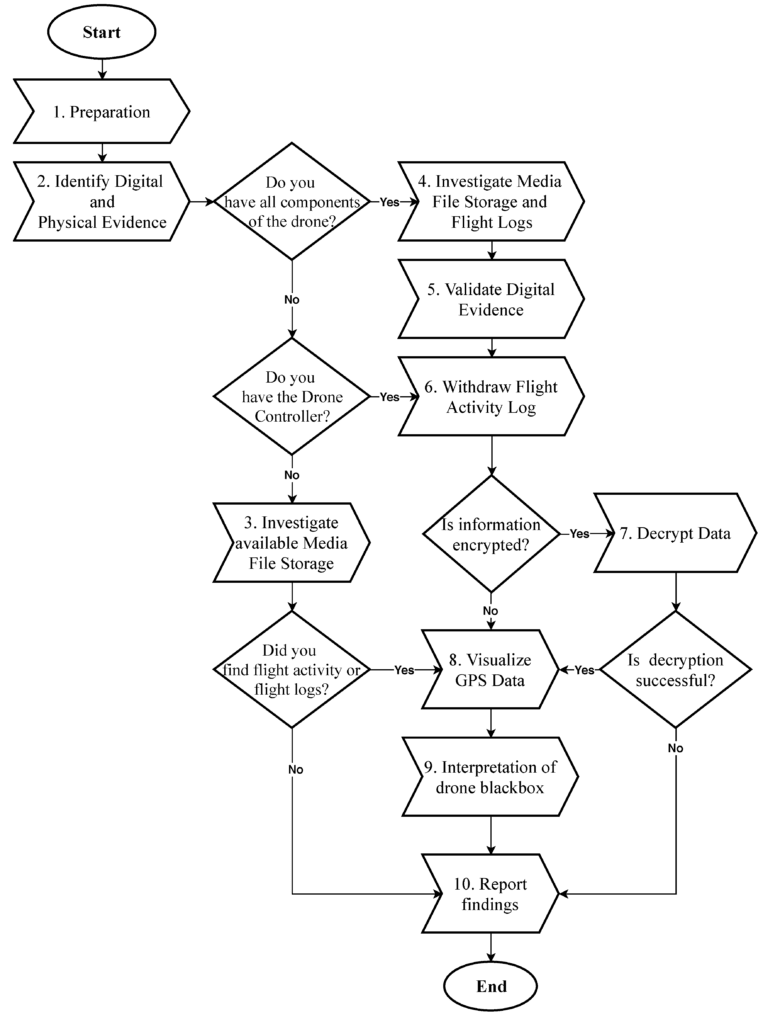
Proposed drone technical forensic investigation process.
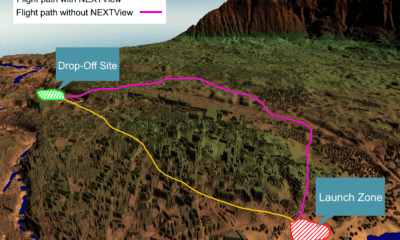
According to the team tools such as ExifTool 11.10, Winhex 16.7, MediaInfo 18.8.1, and 010 Editor 8.0.1 were helpful in analyzing the content of exported media files recovered from drone components. The team also used Autopsy 4.6.0 to export flight logs from the controller chip of the drone to visualize GPS data, using a WebFlightPath python script, a GPS Visualizer, and Google Earth.
The researchers worked to develop a forensic tool which will examine a hypothetical drone case automatically. This case deals with a specific type of drone incident- flying in a restricted area for instance. Assuming that a drone has flown in a no-fly zone and law enforcement officers have seized the drone body only. The question this research answers is: How can we prove flight activities in no-fly zones in a forensically sound manner, and reach the admissibility level against criminals? This requires a tool that can acquire the extracted media files from the drone’s memory storage and process its GPS metadata to match it with no-fly zone location. In the availability of the drone control, it is important for an investigator to conduct behavioural analysis of the flight activity to interpret the “drone black-box” and reach a classification of certain measures to reflect the category of the pilot intention. Hence considering drone anti-forensic and customization techniques are important aspects in drone incident response. Furthermore, an analysis of the secure encryption mechanism of flight logs is crucial on all commercial RPASs to enhance admissibility of drone digital evidence.
The team is currently developing open source tools which can analyze different atoms of media files as well as analyzing digital evidence found on drones to enhance the validation procedure of digital evidence.
Citation: RPAS Forensic Validation Analysis Towards a Technical Investigation Process: A Case Study of Yuneec Typhoon H, Fahad E. Salamh, Umit Karabiyi and Marcus K. Rogers, Sensors 2019, 19(15), 3246; https://doi.org/10.3390/s19153246, https://www.mdpi.com/1424-8220/19/15/3246/htm