Brands
Security Experts Find Vulnerabilities in DJI’s Drone Platform
Researchers at Check Point® Software Technologies Ltd. and DJI, the world’s leader in civilian drones and aerial imaging technology, have shared details of a potential vulnerability that could have impacted DJI’s infrastructure, if exploited.
Check Point Software Technologies is a provider of cyber security solutions to governments and corporate enterprises globally. Its solutions aim to protect customers from cyber-attacks, malware, ransomware and other types of attacks.
In a report submitted in accordance with DJI’s Bug Bounty Program, Check Point Research outlined the process in which an attacker could have potentially gained access to a user’s account through a vulnerability discovered in the user identification process within DJI Forum, a DJI-sponsored online forum about DJI products.
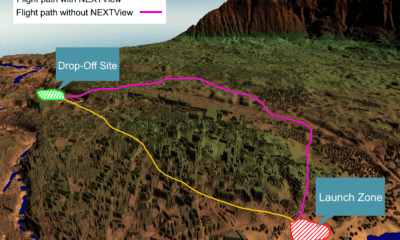
Check Point’s researchers discovered that DJI’s platforms used a token to identify registered users across different aspects of the customer experience, making it a target for hackers looking for ways to access accounts.
DJI consumer users who had synced their flight records, including photos, videos and flight logs to DJI’s cloud servers, and DJI corporate users who used DJI FlightHub software, which includes a live camera, audio and map view, could have become vulnerable.
This vulnerability has since been patched and there is no evidence it was ever exploited.
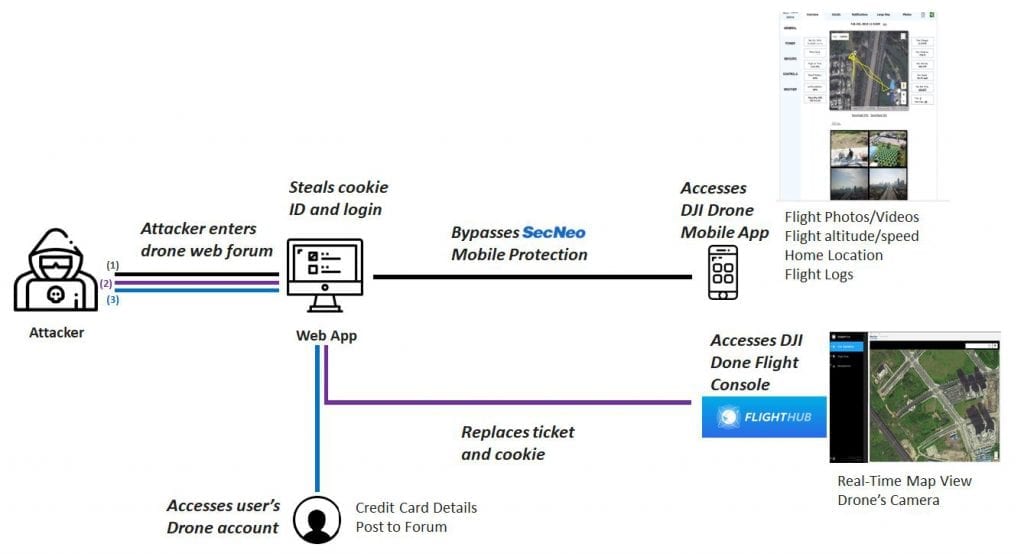
Credit: Check Point Software Technologies Ltd.
“We applaud the expertise Check Point researchers demonstrated through the responsible disclosure of a potentially critical vulnerability,” said Mario Rebello, Vice President and Country Manager, North America at DJI. “This is exactly the reason DJI established our Bug Bounty Program in the first place. All technology companies understand that bolstering cyber security is a continual process that never ends. Protecting the integrity of our users’ information is a top priority for DJI, and we are committed to continued collaboration with responsible security researchers such as Check Point.”
“Given the popularity of DJI drones, it is important that potentially critical vulnerabilities like this are addressed quickly and effectively, and we applaud DJI for doing just that,” said Oded Vanunu, Head of Products Vulnerability Research at Check Point. “Following this discovery, it is important for organizations to understand that sensitive information can be used between all platforms and, if exposed on one platform, can lead to compromise of global infrastructure.”
DJI engineers reviewed the report submitted by Check Point and, in accordance with its Bug Bounty Policy, marked it as high risk/low probability. This is due to a set of preconditions that need to be met before a potential attacker could exploit it.
DJI customers should always use the most current version of the DJI GO or GO 4 pilot apps.
Check Point and DJI advise all users to remain vigilant whenever exchanging information digitally. Always practice safe cyber habits when engaging with others online, and question the legitimacy of links to information seen on user forums and websites.
A full technical analysis of this vulnerability is available from the Check Point Research blog: https://research.checkpoint.com/dji-drone-vulnerability/